In today’s digital age, online safety is a crucial concern for people of all ages, especially seniors. With the rapid advancements in technology, it is essential for seniors to stay informed and equipped with the necessary tools to protect themselves online. Whether it be avoiding scams, protecting personal information, or navigating social media, this article provides a comprehensive guide to help seniors master online safety and confidently navigate the world wide web.
This image is property of www.vpnmentor.com.
Understanding Online Safety
In today’s digital age, online safety has become an essential part of our lives. As more and more aspects of our daily routines migrate to the digital realm, it’s crucial to understand why online safety is important and the potential risks associated with online activities. By educating yourself about the types of online threats lurking on the internet, you can take proactive steps to protect your personal information and ensure a safer online experience.
Why online safety is important
Online safety is important for numerous reasons. First and foremost, it helps protect your personal and financial information from falling into the wrong hands. With the rise of cybercrime and identity theft, taking precautions to safeguard your sensitive data has never been more critical.
Moreover, online safety promotes a safe online environment for everyone. By employing secure practices and being aware of potential online threats, you not only protect yourself but those around you as well. It’s a collective effort to keep the internet a safer place for everyone to use and enjoy.
Risks associated with online activities
Engaging in various online activities exposes you to a range of potential risks. Hackers and cybercriminals are constantly on the lookout for vulnerabilities to exploit, and being unaware of these risks can leave you susceptible to their schemes. Some common risks associated with online activities include:
-
Phishing scams: These fraudulent attempts to obtain sensitive information like usernames, passwords, and credit card details can happen via email, text messages, or even phone calls. Falling for a phishing scam can lead to financial loss or identity theft.
-
Malware and viruses: Clicking on suspicious links or downloading files from untrustworthy sources can infect your devices with malicious software, compromising their security and potentially leading to data loss or unauthorized access.
-
Identity theft: Without proper precautions, your personal information can be easily stolen or misused by cybercriminals, leading to financial damage and reputational harm.
-
Online scams: There are various types of online scams, ranging from fake online shopping sites to fraudulent investment schemes. Falling for these scams can result in significant financial loss.
By being aware of these risks and implementing safety measures, you can mitigate the chances of becoming a victim and navigate the online world with confidence.
Types of online threats
The internet is plagued with various types of online threats, each posing its own set of risks. It’s crucial to familiarize yourself with these threats to better understand the measures you need to take to protect yourself online. Some common types of online threats include:
-
Malware: This term encompasses different types of malicious software, including viruses, worms, and Trojans. Malware can infect your devices and cause harm, such as stealing your personal information or rendering your system inoperable.
-
Phishing: As mentioned earlier, phishing scams involve tricking individuals into providing their sensitive information. Phishing attempts can be sophisticated, often mimicking legitimate websites or disguising themselves as trusted entities, making them difficult to spot.
-
Identity theft: This threat occurs when someone steals your personal information, such as your name, address, social security number, or financial details, with the intent to commit fraud or other criminal activities.
-
Online scams: From fake online shopping websites to Ponzi schemes, online scams come in various forms. They often entice victims with attractive deals or promises of high returns, only to disappear with their money.
-
Social engineering: This technique relies on manipulating individuals into divulging confidential information or performing actions that they wouldn’t normally do. Social engineering attacks can take the form of phone calls, impersonation, or deceptive emails.
By understanding the different types of online threats, you can equip yourself with the knowledge to identify and avoid potential dangers while navigating the digital landscape.
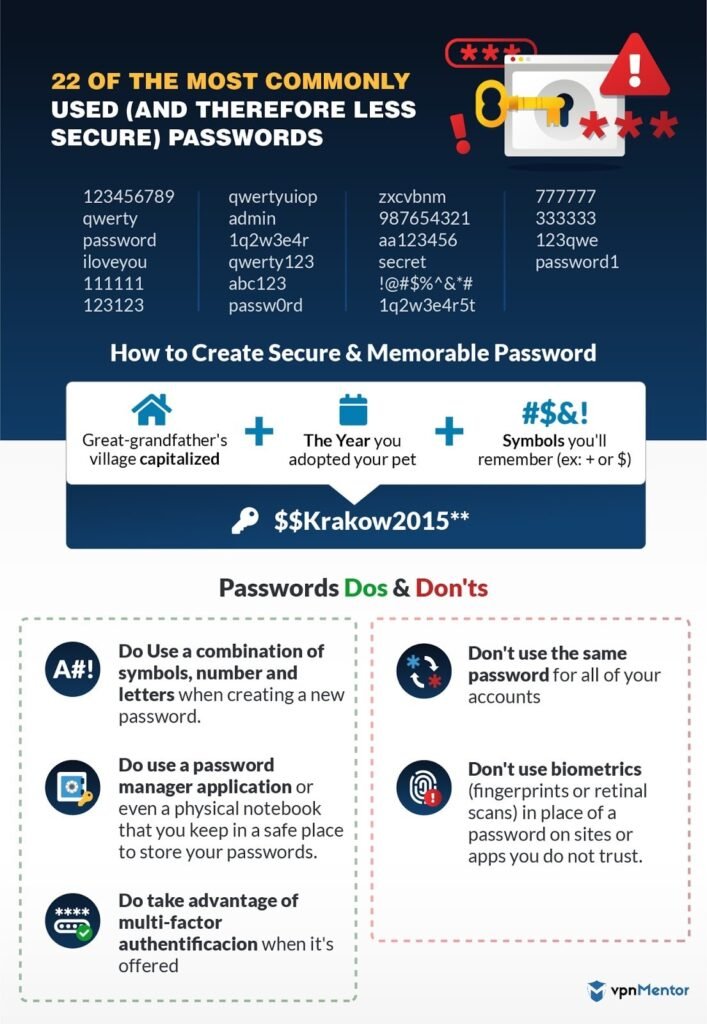
Creating Secure Passwords
Password security plays a significant role in safeguarding your online accounts and personal information. Far too often, weak or easily guessable passwords expose individuals to the risk of unauthorized access. By following best practices and creating strong passwords, you can significantly enhance your online security.
The importance of strong passwords
A strong password acts as a robust barrier against unauthorized access to your accounts. It should be unique and complex, making it difficult for hackers to crack. With weak passwords, such as “password123” or “12345678,” cybercriminals can easily gain access to your accounts, compromising your sensitive information.
Tips for creating a secure password
Creating a strong password doesn’t have to be a complicated task. By following these tips, you can ensure that your passwords are more secure:
-
Length: Opt for passwords that are at least eight characters long. The longer the password, the harder it is for hackers to crack.
-
Complexity: Include a combination of uppercase and lowercase letters, numbers, and special characters in your password. Avoid common dictionary words or easily guessable patterns.
-
Avoid personal information: Don’t use personal information like your name, birthday, or address in your passwords. Hackers can easily obtain this information through various means.
-
Unique passwords: Use a different password for each of your accounts. Reusing passwords across multiple platforms can put all of your accounts at risk if one password is compromised.
Using password managers
Remembering multiple complex passwords can be a daunting task. That’s where password managers come in handy. These tools securely store all your passwords and automatically fill them in for you when needed. Password managers also generate strong, unique passwords for all your accounts, eliminating the need for you to come up with and remember them all. With the help of a password manager, you only need to remember one master password to access all your other passwords securely.
By creating and managing secure passwords, you create a stronger defense against unauthorized access to your accounts and personal information.
Recognizing and Avoiding Phishing Scams
Phishing scams continue to be a prevalent threat in the online world, targeting unsuspecting individuals with the goal of stealing their personal information or money. Recognizing the signs of a phishing scam and knowing how to avoid falling victim to them is essential in maintaining your online safety.
What is phishing?
Phishing is a type of cyber attack that involves tricking individuals into revealing their sensitive information. It often occurs through deceptive emails, text messages, or phone calls that appear to come from legitimate sources like banks, government agencies, or well-known companies. The goal is to deceive recipients into clicking on malicious links or providing their personal information, such as usernames, passwords, or credit card details.
Common signs of a phishing scam
While some phishing attempts can be sophisticated and difficult to identify, there are several common signs to look out for:
-
Generic greetings: Phishing emails often use generic greetings like “Dear Customer” instead of addressing you by your name.
-
Urgency or threats: Phishing emails often contain urgent or threatening language, pressuring you to take immediate action. They may claim that your account will be closed or that you will face legal consequences if you don’t provide your information.
-
Poor grammar and spelling mistakes: Phishing emails often contain multiple grammar and spelling errors, indicating a lack of professionalism or attention to detail.
-
Suspicious sender email address: Check the sender’s email address carefully. Phishing emails often come from addresses that closely resemble legitimate ones but have slight differences or misspellings.
-
Suspicious links or attachments: Be cautious of any links or attachments in emails or messages, especially if they are unexpected or from unknown sources. These could lead to malicious websites or infect your device with malware.
Tips to avoid falling for a phishing scam
Protecting yourself from phishing scams requires a combination of vigilance and cautiousness. Here are some tips to help you avoid falling victim to these deceptive schemes:
-
Verify the source: Independently verify the sender’s identity by contacting the company or organization directly through their official website or phone number. Do not click on any links or call any numbers provided in the suspicious email or message.
-
Be skeptical of urgent requests: Phishing emails often use urgency to create panic and pressure individuals into making hasty decisions. Take a step back and evaluate the situation critically. Legitimate organizations will not ask for sensitive information through email.
-
Check website security: Before entering any personal information on a website, ensure that it is secure. Look for the padlock symbol in the address bar and confirm that the website’s URL begins with “https://” rather than just “http://”.
-
Keep your software up to date: Regularly update your operating system and applications, as these updates often include security patches that protect against known vulnerabilities.
-
Invest in security software: Install reputable antivirus and anti-malware software to detect and block potential threats on your devices.
By staying vigilant, practicing skepticism, and following these tips, you can greatly reduce the risk of falling for phishing scams and mitigate the potential damage they can cause.
Protecting Personal Information
In the digital age, the value of personal information cannot be overstated. From financial details to social security numbers, your personal information is highly sought after by cybercriminals. By understanding the value of personal information, adopting best practices for sharing it online, and taking steps to protect against identity theft, you can safeguard your privacy and minimize the risk of falling victim to cybercrime.
Understanding the value of personal information
Cybercriminals are constantly looking for personal information that can be sold or used to commit fraud. Your personal information, including your name, address, phone number, social security number, and financial details, is highly valuable to them. With this information, they can open credit accounts, make online purchases, or even assume your identity, causing significant financial and reputational harm.
Best practices for sharing personal information online
While it’s impossible to avoid sharing personal information online entirely, you can adopt best practices to minimize the risk of that information falling into the wrong hands:
-
Be cautious on social media: Limit the amount of personal information you share on social media platforms. Avoid posting your full name, address, phone number, or other sensitive details that can be used to identify or locate you.
-
Privacy settings: Take advantage of the privacy settings available on social media platforms to control who can see your personal information and posts. Regularly review and update these settings to ensure they align with your desired level of privacy.
-
Avoid oversharing: Be mindful of the information you share online, especially in public forums or discussion boards. Avoid disclosing sensitive details or engaging in discussions that could expose personal information.
-
Be wary of public Wi-Fi: When connecting to public Wi-Fi networks, be cautious about the information you transmit. Avoid accessing sensitive accounts or sharing personal information while connected to public networks, as they may be insecure and susceptible to interception.
Protecting against identity theft
Identity theft can have devastating consequences, both financially and emotionally. To protect yourself against this risk, consider taking the following precautions:
-
Monitor financial statements: Regularly review your bank and credit card statements for any suspicious activity. Report any unauthorized transactions immediately to your financial institution.
-
Check your credit report: Obtain a free copy of your credit report from each of the major credit bureaus annually. This will allow you to review your credit history for any unauthorized accounts or suspicious activity.
-
Use strong, unique passwords: As discussed earlier, strong passwords are your first line of defense against unauthorized access. Use a unique password for each of your accounts and avoid using easily guessable information.
-
Enable two-factor authentication: Whenever possible, enable two-factor authentication on your accounts. This adds an extra layer of security by requiring a second verification step, such as a code sent to your phone or email, when logging in.
Protecting your personal information involves a combination of awareness, caution, and proactive measures. By implementing these best practices, you can reduce the risk of identity theft and potential financial loss.

This image is property of www.safetydetectives.com.
Securing Wi-Fi Networks
Securing your Wi-Fi network is crucial to protect your devices and personal information from unauthorized access. With the rise of smart homes and connected devices, ensuring the security of your Wi-Fi network has become more important than ever. By understanding why secure Wi-Fi is essential, changing default router settings, and creating strong Wi-Fi passwords, you can establish a safer online environment for yourself and those within your network.
Why secure Wi-Fi is essential
Securing your Wi-Fi network is essential for several reasons. An unsecured Wi-Fi network can:
-
Allow unauthorized access: Without proper security measures, anyone within range can connect to your Wi-Fi network, potentially accessing your personal information or using your network for illegal activities.
-
Compromise your devices: An unsecured Wi-Fi network can expose your devices to malware or other malicious attacks. Once inside your network, cybercriminals can access and compromise your connected devices, including computers, smartphones, and smart home devices.
-
Slow down your internet speed: If unauthorized devices are connected to your Wi-Fi network, they can consume your bandwidth and slow down your internet speed.
Changing default router settings
When setting up a new Wi-Fi router, it’s crucial to change the default settings to enhance security. Default settings often use generic passwords and network names, making it easier for hackers to gain unauthorized access. Here are some steps to secure your router:
-
Change the administrator password: Access your router’s settings by entering its IP address in a web browser. Locate the administrator or login settings and change the default password to a strong, unique one.
-
Disable remote management: Remote management allows you to access and configure your router from outside your home network. While convenient, it also poses a security risk. Disable remote management unless absolutely necessary.
-
Enable encryption: Enable WPA2 or WPA3 encryption, which secures the data transmitted over your Wi-Fi network. These encryption protocols are more secure than WEP (Wired Equivalent Privacy) and should be the preferred choice.
-
Change the network name (SSID): Avoid using personal information or easily identifiable details in your Wi-Fi network name. Choose a unique name that doesn’t reveal anything about you or your location.
Tips for creating a strong Wi-Fi password
A strong Wi-Fi password is crucial for preventing unauthorized access to your network. Here are some tips for creating a strong Wi-Fi password:
-
Length: Aim for a password that is at least 12 characters long. The longer the password, the harder it is to crack.
-
Complexity: Include a combination of uppercase and lowercase letters, numbers, and special characters. Avoid predictable patterns or easily guessable information.
-
Avoid personal information: Don’t use personal information like your name, address, or birthdate in your Wi-Fi password. Personal information can be easily obtained through various means.
-
Unique password: Use a completely different password for your Wi-Fi network than you use for other accounts. Reusing passwords across multiple platforms can put all your accounts at risk if one password is compromised.
By securing your Wi-Fi network and creating a strong password, you can significantly reduce the risk of unauthorized access to your personal information and devices.
Using Antivirus Software
Antivirus software is an essential tool for protecting your devices from malware, viruses, and other online threats. With new forms of cyber threats emerging every day, having reliable antivirus software is crucial in maintaining your online safety. By understanding the importance of antivirus software, choosing the right one for your needs, and keeping your software updated and regularly scanned, you can effectively bolster your device’s security.
The importance of antivirus software
Antivirus software provides a vital layer of defense against various online threats, including malware, viruses, and spyware. Here’s why antivirus software is important:
-
Malware protection: Antivirus software scans your files, emails, and web traffic for any signs of malware. It helps detect and remove malicious software, preventing it from causing harm to your device or compromising your personal information.
-
Real-time protection: Many antivirus programs run in the background, continuously monitoring your device for any suspicious activity. If it detects anything out of the ordinary, it alerts you and takes action to neutralize the threat.
-
Phishing and scam protection: Some antivirus software includes features that help identify and block phishing websites or scam emails, providing an extra layer of protection against these common threats.
Choosing the right antivirus software
With countless antivirus options available in the market, selecting the right one can be overwhelming. When choosing antivirus software, consider the following factors:
-
Reputation and reviews: Look for reputable antivirus software with positive reviews from both experts and users. Research different options and compare their features and performance.
-
Compatibility: Ensure that the antivirus software is compatible with your operating system and device specifications. Some software is specifically designed for Windows, while others cater to Mac or mobile devices.
-
Features: Evaluate the features offered by each antivirus program. Look for features like real-time scanning, automatic updates, and web protection to enhance your device’s security.
-
Ease of use: Consider user-friendliness and ease of navigation when selecting antivirus software. A complex or confusing interface can make it difficult to manage and configure the software effectively.
Updating and scanning regularly
Installing antivirus software isn’t enough; you must also keep it up to date and run regular scans to maintain its effectiveness. Follow these practices:
-
Automatic updates: Enable automatic updates for your antivirus software to ensure that it receives the latest security patches and virus definitions. This helps protect against emerging threats.
-
Regular scanning: Schedule regular scans of your device to proactively detect and eliminate any malware or viruses. Set up scans during periods when you’re not actively using your device to avoid interruptions.
-
Keep your operating system and applications up to date: Antivirus software works in conjunction with your operating system and other applications. Regularly update your operating system and applications to ensure you have the latest security patches installed.
By choosing the right antivirus software, keeping it updated, and running regular scans, you can significantly enhance your device’s security and protect against the constantly evolving landscape of online threats.
This image is property of static.safetydetectives.com.
Safe Practices for Online Shopping
Online shopping offers convenience and accessibility, allowing you to purchase products and services from the comfort of your home. However, it’s important to follow safe practices to ensure a secure online shopping experience. By using secure payment methods, verifying the legitimacy of online vendors, and following tips for safe online transactions, you can shop online with confidence.
Secure payment methods
When it comes to online shopping, it’s crucial to choose secure payment methods to protect your financial information. Here are some commonly used secure payment methods:
-
Credit cards: Credit cards offer protection against fraudulent charges and unauthorized transactions. Many credit card companies have robust security measures in place and offer zero-liability policies for unauthorized charges.
-
Digital wallets: Digital wallets, such as Apple Pay, Google Pay, or PayPal, provide an extra layer of security by encrypting your payment information and allowing you to make purchases without directly sharing your credit card details with the merchant.
-
Virtual credit cards: Some financial institutions offer virtual credit cards that allow you to generate a unique credit card number for each online transaction. This adds an extra layer of security, as the virtual credit card number cannot be used for subsequent transactions.
Verifying the legitimacy of online vendors
Before making a purchase from an online vendor, it’s important to verify their legitimacy to avoid falling victim to scams or receiving counterfeit products. Here’s how to do it:
-
Research the vendor: Conduct a quick online search to gather information about the vendor. Look for customer reviews, ratings, and any negative experiences shared by others.
-
Check for secure website indicators: Before entering any personal or payment information, ensure that the website is secure. Look for the padlock symbol in the address bar and verify that the website’s URL begins with “https://”.
-
Familiarize yourself with return policies: Read and understand the vendor’s return policy, as it can be an indicator of their legitimacy. Legitimate vendors usually provide clear instructions on returns and refunds.
Tips for safe online transactions
To ensure safe online transactions, follow these tips:
-
Use a secure and private network: Avoid making online purchases when connected to public Wi-Fi networks, as they can be insecure and susceptible to interception. Use a private and secure network to protect your personal and financial information.
-
Keep your devices updated: Regularly update your operating system and applications to ensure you have the latest security patches installed. Outdated software can leave your device vulnerable to cyber threats.
-
Be cautious of deals that are too good to be true: If a deal seems too good to be true, it probably is. Be wary of websites offering significantly lower prices compared to reputable sellers, as they may be selling counterfeit products or attempting to scam you.
By following these safe practices for online shopping, you can minimize the risk of fraud, protect your financial information, and have a more enjoyable shopping experience.
Avoiding Online Scams
Online scams come in various forms, preying on unsuspecting individuals and exploiting their trust or vulnerabilities. From phishing scams to fake tech support calls, staying informed and vigilant is crucial in avoiding falling victim to these scams. By understanding different types of online scams, recognizing warning signs, and following tips to avoid falling for online scams, you can protect yourself from financial loss and other potential harm.
Different types of online scams
Online scams can take many forms. Here are some common types of scams to watch out for:
-
Phishing scams: Phishing scams typically involve fraudulent emails, text messages, or phone calls impersonating legitimate organizations to trick individuals into providing their personal or financial information.
-
Fake online shopping sites: Scammers create professional-looking websites offering enticing deals on popular products. However, once payment is made, the products never arrive, or the items received are counterfeit.
-
Advanced fee fraud: This scam involves promising a large sum of money or a significant reward in exchange for a small fee upfront. However, once the fee is paid, the promised reward never materializes.
-
Tech support scams: Scammers pose as tech support representatives and contact individuals claiming that their computer is infected with malware or experiencing other issues. They convince victims to grant them remote access or pay for unnecessary services.
Warning signs of online scams
While scammers are becoming increasingly sophisticated, there are several warning signs to look out for:
-
Unsolicited communication: Be cautious of unsolicited emails, text messages, or phone calls, especially if they request personal or financial information.
-
Urgency or pressure: Scammers often create a sense of urgency or pressure to push you into making hasty decisions. They may claim that you have a limited time to respond or that dire consequences will occur if you don’t comply.
-
Requests for payment in advance: Be skeptical of requests for payment in advance, especially if the promised product or service hasn’t been delivered yet. Legitimate sellers typically ask for payment upon the delivery of goods or services.
-
Poor grammar and spelling mistakes: Scam messages often contain multiple grammar and spelling errors, as scammers may operate in countries where English is not their first language.
Tips to avoid falling for online scams
Protecting yourself from online scams requires a combination of skepticism and caution. Here are some tips to avoid falling for these scams:
-
Be cautious of unsolicited communication: Don’t share personal or financial information in response to unsolicited requests. Legitimate organizations will never ask for sensitive information through email or text.
-
Verify before you trust: Independently verify the legitimacy of the sender or the organization before taking any action. Reach out to the organization directly through their official website or phone number to confirm the communication’s authenticity.
-
Educate yourself: Stay informed about various online scams and the strategies scammers employ. Recognizing common warning signs can help you identify potential scams more easily.
-
Use reputable sources: Only make online purchases or provide personal information through reputable websites. Look for secure website indicators, such as the padlock symbol and “https://” in the URL.
By being vigilant and cautious, you can avoid falling for online scams and protect yourself from financial loss and potential harm.

This image is property of www.getcybersafe.gc.ca.
Safe Social Media Usage
Social media platforms have become an integral part of our lives, connecting us with friends, family, and the global community. However, it’s important to practice safe social media usage to protect your privacy and personal information. By setting privacy controls, recognizing and avoiding fake profiles, and being selective with friend requests and connections, you can navigate social media safely and responsibly.
Setting privacy controls on social media platforms
Social media platforms provide various privacy settings that allow you to control who can see your posts and access your personal information. Consider implementing the following privacy measures:
-
Customize your privacy settings: Review the privacy settings of each social media platform you use and configure them according to your preferences. Limit the visibility of your posts and personal information to only those you trust.
-
Be cautious about sharing personal details: Avoid posting sensitive information, such as your full name, address, phone number, or financial details, on your social media profiles. The less information you share publicly, the better.
-
Monitor tags and mentions: Regularly check for tags or mentions of your name on social media and adjust the settings to review and approve them before they appear on your profile. This helps prevent others from sharing potentially harmful or inaccurate content on your behalf.
Recognizing and avoiding fake profiles
Fake profiles or impostor accounts are prevalent on social media platforms, used for various malicious purposes. Learning how to identify and avoid fake profiles is essential for your online safety. Here are some signs of fake profiles:
-
Lack of personal information: Fake profiles often have sparse or incomplete personal information. Look for missing details, inconsistent employment history, or lack of connections to genuine users.
-
Suspicious profile picture: Be wary of profiles with overly perfect or stock photos, as fake accounts often use generic images instead of personal photos.
-
Unusual behavior or excessive friend requests: If you receive friend requests from unknown individuals with no mutual connections, it raises suspicion. Fake profiles may also engage in unusual or aggressive behavior, such as spamming or soliciting.
Being selective with friend requests and connections
Being mindful of who you accept as friends or connections on social media can greatly impact your online safety. Here are some tips to consider:
-
Only accept requests from people you know: Be cautious of accepting friend requests or connection requests from unknown individuals. Verify their identity and consider the appropriateness of connecting with them.
-
Regularly review and prune your connections: Periodically review your friend list or connections and remove individuals you no longer have a legitimate reason to be connected with. This helps reduce the chances of accidental exposure to potentially harmful content.
-
Be cautious with sharing personal information privately: Even if you trust your connections, avoid sharing sensitive or private information through direct messages or private chats. Messages can be screenshotted or inadvertently shared with others.
By following these safe practices for social media usage, you can enjoy the benefits of connecting with others while protecting your privacy and personal information.
Staying Up to Date with Security Updates
Staying up to date with security updates is a crucial aspect of maintaining online safety. Cyber threats and vulnerabilities are constantly evolving, and software updates incorporate patches to address these vulnerabilities. By understanding the significance of software updates, configuring automatic updates, and regularly checking for updates on devices and applications, you can ensure that your devices remain protected.
The importance of software updates
Software updates play a pivotal role in maintaining the security of your devices. Here’s why staying up to date with security updates is essential:
-
Patching vulnerabilities: Updates often include security patches to address vulnerabilities that cybercriminals can exploit. Failing to update your software leaves your devices susceptible to known threats.
-
Bug fixes and performance improvements: In addition to security patches, software updates also include bug fixes and performance enhancements. These updates help improve the stability and overall functionality of your devices.
-
Improved compatibility: Updates may introduce compatibility with new technologies, devices, or file formats. Staying up to date ensures that your devices can seamlessly interact with the latest software and hardware.
Configuring automatic updates
Configuring automatic updates is a convenient way to ensure that your devices receive the latest security patches and bug fixes without requiring manual intervention. Here’s how to enable automatic updates on different devices:
-
Operating systems (Windows, macOS, Linux): Most operating systems have built-in options to enable automatic updates. Locate the update settings within your device’s system preferences or settings, and choose the automatic update option.
-
Mobile devices (iOS, Android): On mobile devices, you can enable automatic updates through the device settings. For iOS devices, navigate to Settings > General > Software Update, and enable “Download iOS updates automatically” or “Customize Automatic Updates.” On Android devices, go to Settings > System > Advanced > System updates, and enable “Automatic system updates.”
-
Applications: Many applications, including web browsers and productivity software, have automatic update settings. Check the settings within each application to ensure that automatic updates are enabled.
Checking for updates on devices and applications
While enabling automatic updates is recommended, it’s important to periodically check for updates manually. Some updates may require user consent, and not all devices or applications support automatic updates. Here’s how to manually check for updates:
-
Operating systems: Most operating systems have a built-in mechanism to check for updates manually. Navigate to the update settings within your device’s system preferences or settings, and look for an option to check for updates.
-
Mobile devices: On iOS devices, you can manually check for updates by going to Settings > General > Software Update and selecting “Check for Update.” On Android devices, access Settings > System > Advanced > System updates, and tap on “Check for updates.”
-
Applications: Within each application, there is usually an option in the settings or preferences menu to check for updates. Look for an option similar to “Check for updates” or “Update now.”
By staying up to date with security updates, you ensure that your devices remain protected against the latest threats and vulnerabilities. Additionally, by enabling automatic updates, you minimize the risk of missing critical updates due to oversight or forgetfulness.
In conclusion, understanding online safety and adopting secure practices is essential in safeguarding your personal information and protecting yourself from various online threats. By recognizing the importance of online safety, creating secure passwords, avoiding phishing scams, protecting personal information, securing Wi-Fi networks, using antivirus software, practicing safe online shopping, staying vigilant against online scams, using social media safely, and staying up to date with security updates, you can navigate the online world with confidence. Taking these proactive measures is key to ensuring a safer and more enjoyable online experience for you and those around you. Stay safe!
This image is property of www.vpnmentor.com.
